Authentication and authorization
People who are registered as users have the right to access Neptune DXP - Open Edition. Those users can be organized into groups. The type of activities that users can perform is determined by their roles.
You can manage users access to Neptune DXP - Open Edition tools and application. User authentication and authorization processes in Neptune DXP - Open Edition ensure that users can access only the resources to which they have the required permissions.
Authentication
Authentication is the process of verifying the users identity. Typically, this entails obtaining the username and a password or some other credential from the user.
Access control, normally based on the identity of the user who requests access to a resource, is essential to effective security. The launchpad uses different authentication methods.
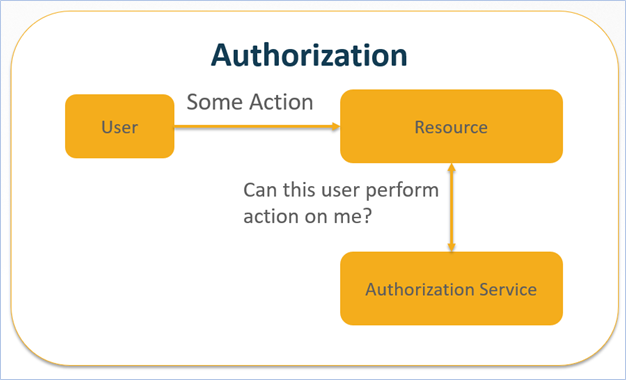
Authorization
Authorization is the process of verifying whether a user has access to protected resources. It is the process by which the system determines what level of access an authenticated user should have to secured resources.
Authentication and authorization in Neptune DXP - Open Edition
Authentication sources
-
User ID/Password (Local): Typically used for test accounts or training accounts.
-
User ID/Password (LDAP): End user accounts.
-
Digital Certificates (SAML): Example: Ping ID, Salesforce, …
-
Anonymous: Used to access anonymous pages (for example, privacy policy, external available public content)
Authorization process
All content, for example, apps or tiles, is under administrative control of Neptune DXP - Open Edition. Admin content is controlled with an access control lists (ACL).
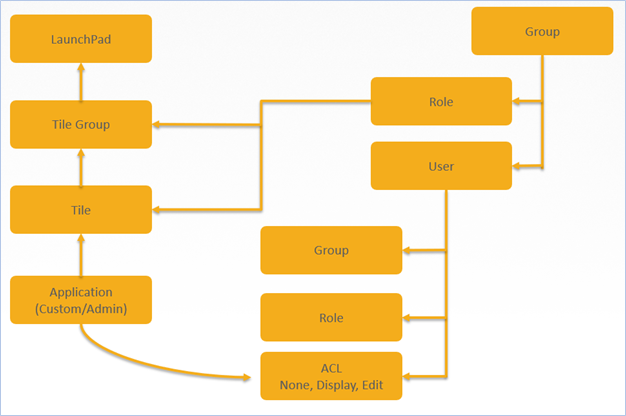
User management object mapping
For launchpad and applications, access management roles and groups are assigned to the authentication of the users:
- Launchpad
-
It is a container for apps and includes tile groups.
- Tile group
-
Tile groups include tiles, roles can be assigned to the tile group.
- Tile
-
Each tile represents one application, roles can be assigned to the tile.
- Groups
-
Users can be assigned to no, one, or more group. A group of users simplifies the assignment of users to tasks. For example, a "Help Desk" process may involve a pool of customer support clerks, all belonging to a group named "Customer Support". It is the highest level security object.
- Role
-
Role makes it possible to define customized roles with different levels of permission so that the functions and privileges of different users can be easily controlled and managed. A role can be assigned to a tile group and tile.
- User
-
User can include groups, roles, ACL.
- ACL
-
Access control list.